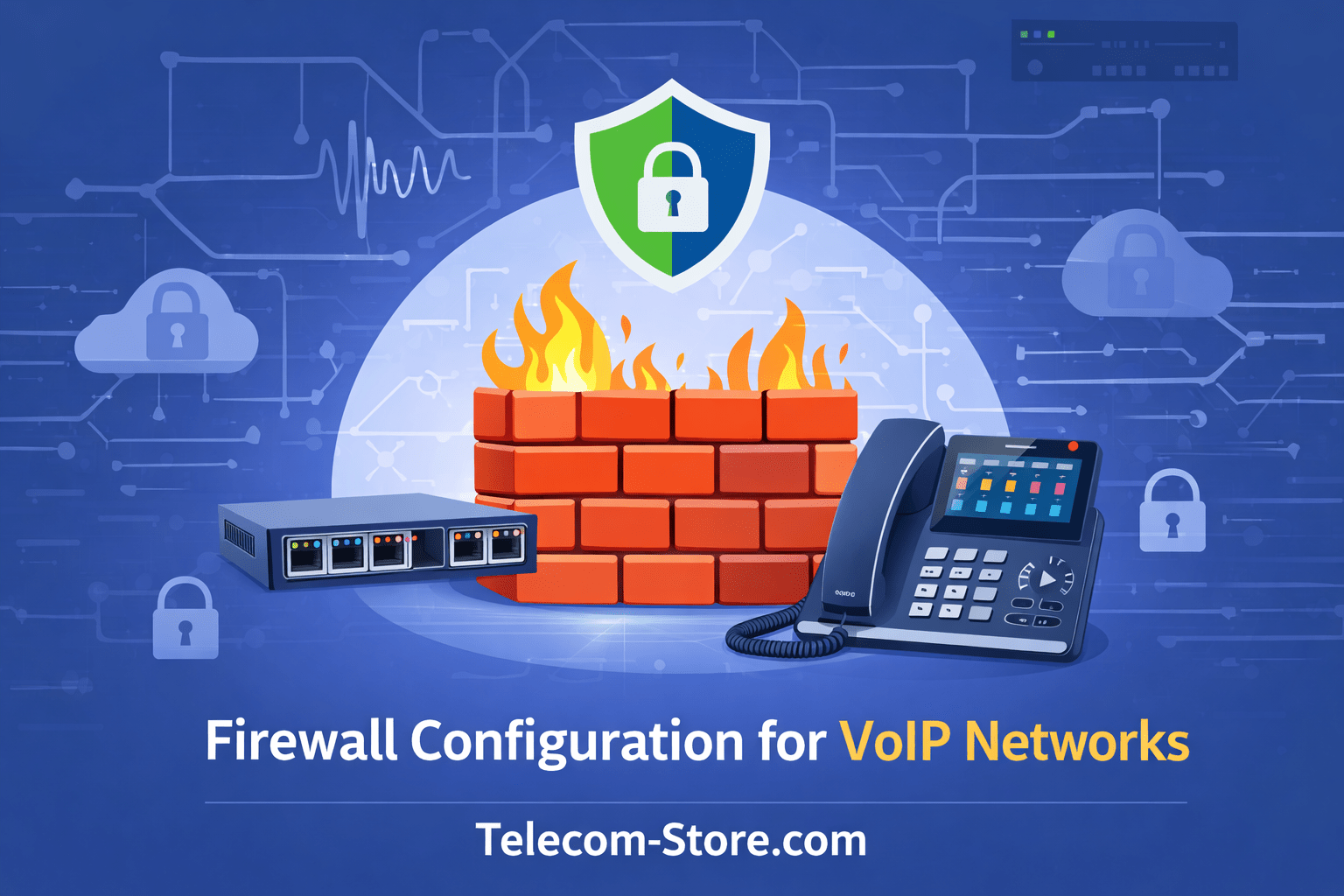
Why Firewall Configuration Matters for VoIP
Firewall configuration for VoIP is one of the most overlooked factors affecting call quality and system reliability. Many small businesses deploy VoIP systems but experience issues like dropped calls, one-way audio, or failed registrations. In most cases, the root cause is not the phone system itself—it’s the network firewall.
A properly configured firewall ensures that VoIP traffic flows efficiently while still protecting the network from unauthorized access. Striking that balance is essential for maintaining both performance and security.
How VoIP Traffic Works on a Network
Before configuring a firewall, it’s important to understand how VoIP communicates across a network.
Key VoIP Protocols
- SIP (Session Initiation Protocol) – Handles call setup and signaling
- RTP (Real-Time Transport Protocol) – Carries the actual voice audio
- SRTP – Secure version of RTP
- TLS – Encrypts SIP signaling
Ports Commonly Used
- SIP: UDP/TCP 5060, TLS 5061
- RTP: Typically UDP 10000–20000 (varies by system)
Firewalls must allow this traffic in a controlled way. Blocking or misrouting these ports leads directly to call issues.
Common Firewall Issues in VoIP Deployments
Small business VoIP setups often run into predictable firewall-related problems:
One-Way Audio
Usually caused by:
- NAT (Network Address Translation) issues
- RTP ports not properly opened
Failed Registration
Occurs when:
- SIP traffic is blocked
- Firewall is rewriting packets incorrectly
Dropped Calls
Often linked to:
- Session timeouts
- Improper UDP handling
Core Firewall Configuration Principles for VoIP
1. Disable SIP ALG
Most routers include a feature called SIP ALG (Application Layer Gateway). While intended to help VoIP traffic, it often breaks it.
Recommendation:
- Always disable SIP ALG
2. Use Static Port Forwarding (When Required)
If your PBX is hosted on-premise:
- Forward SIP and RTP ports to your PBX server
- Avoid exposing unnecessary ports
3. Implement Quality of Service (QoS)
QoS prioritizes VoIP traffic over other network activity.
Without QoS:
- Large downloads can degrade call quality
- Latency and jitter increase
4. Restrict Access by IP
Instead of opening SIP ports to the entire internet:
- Allow only your VoIP provider’s IP ranges
- Block all other inbound SIP traffic
This reduces exposure to attacks such as SIP scanning and toll fraud.
Firewall Setup for Cloud-Based PBX Systems
For cloud-hosted systems like FreePBX or hosted VoIP providers, firewall configuration is simpler but still critical.
Outbound Rules
Ensure your network allows:
- SIP traffic to your provider
- RTP streams outbound
Inbound Rules
Typically minimal:
- Responses to outbound requests
- No need to open inbound SIP unless hosting services internally
Hardware Considerations for VoIP Networks
Your firewall and network hardware must support VoIP workloads.
Recommended Features
- Stateful packet inspection
- QoS support
- VLAN capability
- Gigabit throughput
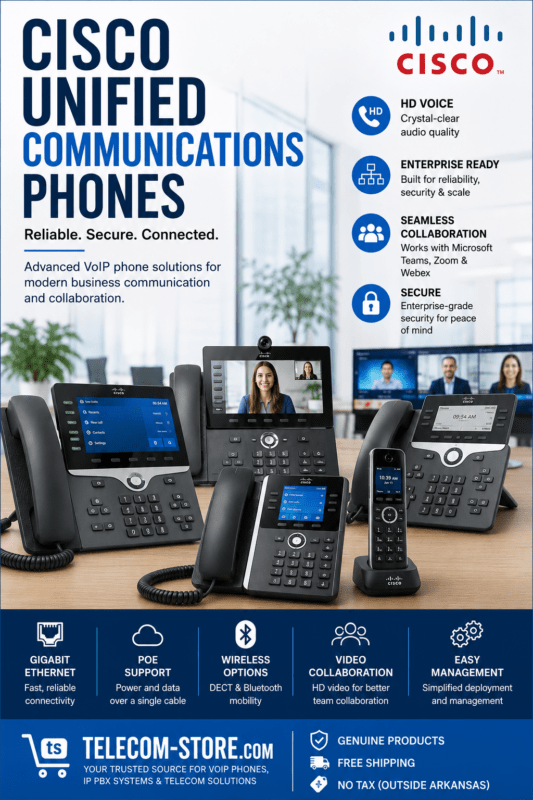
Example VoIP-Compatible Devices
When deploying VoIP phones, selecting compatible hardware is important:
- Yealink T54W
- Yealink T57W
- Yealink T46U
These devices support SIP standards and work well with properly configured firewalls and PBX systems.
Network Segmentation for VoIP
Separating VoIP traffic from general data traffic improves performance and security.
VLAN Configuration
- Create a dedicated VLAN for VoIP devices
- Assign phones and PBX systems to that VLAN
Benefits
- Reduced congestion
- Improved call quality
- Easier troubleshooting
Security Best Practices for VoIP Firewalls
Firewall configuration is not just about performance—it’s also about protection.
Protect Against SIP Attacks
Common threats include:
- Brute-force login attempts
- SIP scanning
- Toll fraud
Recommended Measures
- Use strong authentication
- Change default SIP ports if possible
- Enable intrusion detection systems
- Monitor logs regularly
Buyer Considerations Before Configuring a VoIP Firewall
Compatibility
Ensure your firewall supports:
- SIP-aware traffic handling (without breaking it)
- Required VoIP codecs
- Integration with your PBX system
Setup Requirements
Before deployment, confirm:
- Internet connection with sufficient bandwidth
- Proper router/firewall configuration access
- Knowledge of your VoIP provider’s requirements
Limitations
Even with proper firewall configuration:
- Poor ISP performance can still affect VoIP
- Consumer-grade routers may struggle under load
- Misconfigured NAT can still cause issues
Understanding these limitations helps set realistic expectations.
When to Consider Professional Assistance
Firewall configuration for VoIP can become complex, especially in multi-site or high-call-volume environments.
Working with a provider like
Axion Communications can help ensure your system is configured correctly and securely.
Practical Conclusion
Firewall configuration for VoIP is not optional—it directly impacts call quality, reliability, and security. For small businesses, taking the time to properly configure SIP, RTP, and network priorities can prevent ongoing issues and reduce troubleshooting time later.
A well-configured firewall supports both performance and protection, allowing your VoIP system to operate consistently within your network environment.
FAQ Section
What is firewall configuration for VoIP and why is it important?
Firewall configuration for VoIP involves allowing specific voice traffic while blocking unauthorized access. It ensures calls connect properly and prevents issues like dropped calls or one-way audio. Proper configuration also protects against threats like SIP attacks and unauthorized access attempts.
Do I need to open ports for VoIP to work properly?
Yes, VoIP requires specific ports for SIP signaling and RTP audio streams. These ports must be open or allowed through the firewall. However, access should be restricted to trusted IP addresses to maintain security.
What is SIP ALG and should it be enabled?
SIP ALG is a feature in many routers designed to manage SIP traffic. In practice, it often interferes with VoIP communication. It is generally recommended to disable SIP ALG to avoid connectivity issues.
How does QoS improve VoIP call quality?
Quality of Service (QoS) prioritizes voice traffic over other network data. This reduces latency, jitter, and packet loss, resulting in clearer and more stable calls, especially in busy networks.
Can a firewall cause one-way audio issues in VoIP?
Yes, one-way audio is often caused by firewall or NAT misconfiguration. RTP ports may be blocked or improperly routed, preventing audio from reaching one side of the call.
Is a business-grade firewall necessary for VoIP?
While not strictly required, business-grade firewalls offer better performance, security, and configuration options. They are more reliable for handling VoIP traffic in small business environments.
How can I secure my VoIP system from attacks?
Use strong passwords, restrict SIP access by IP, disable unused services, and monitor logs. Firewall rules should block unauthorized traffic while allowing legitimate VoIP communication.
Does a cloud PBX require firewall configuration?
Yes, even cloud PBX systems require proper firewall setup. Outbound traffic must be allowed, and security settings should still be enforced to protect the network.